Conflicts in the Middle East, Ukraine, and other areas of simmering geopolitical tensions have made policy experts the latest target of cyber operations conducted by state-sponsored groups.
An Iran-linked group — known as Charming Kitten, CharmingCypress, and APT42 — recently targeted Middle East policy experts in the region as well as in the US and Europe, using a phony webinar platform to compromise its targeted victims, incident response services firm Volexity stated in an advisory published this month.
Charming Kitten is well known for its extensive social engineering tactics, including low-and-slow social engineering attacks against think tanks and journalists to gather political intelligence, the firm stated.
The group often dupes is targets into installing Trojan-rigged VPN applications to gain access to the fake webinar platform and other sites, resulting in the installation of malware. Overall, the group has embraced the long confidence game, says Steven Adair, co-founder and president of Volexity.
“I don’t know if that is necessarily sophisticated and advanced, but it is a lot of effort,” he says. “It’s more advanced and more sophisticated than your average attack by a significant margin. It’s a level of effort and dedication … that is definitely different and uncommon … to go to that much effort for such a specific set of attacks.”
Geopolitical Experts in the Crosshairs
Policy experts are a frequently targeted by nation-state groups. The Russia-linked ColdRiver group, for example, has targeted nongovernmental organizations, military officers, and other experts using social engineering to gain the confidence of the victim and then following up with a malicious link or malware. In Jordan, targeted exploitation — reportedly by government agencies — used the Pegasus spyware program developed by the NSO Group and targeted journalists, digital-rights lawyers, and other policy experts.
Other companies have also described Charming Kitten/CharmingCypress’ tactics. In a January advisory, Microsoft warned that the group, which it calls Mint Sandstorm, had targeted journalists, researchers, professors, and other experts covering security and policy topics of interest to the Iranian government.
“Operators associated with this subgroup of Mint Sandstorm are patient and highly skilled social engineers whose tradecraft lacks many of the hallmarks that allow users to quickly identify phishing emails,” Microsoft stated. “In some instances of this campaign, this subgroup also used legitimate but compromised accounts to send phishing lures.”
The group has been active since at least 2013, has strong links to the Islamic Revolutionary Guard Corps (IRGC), and has not been directly involved in the cyber-operational aspect of the conflict between Israel and Hamas, according to cybersecurity firm CrowdStrike.
“Unlike in the Russia-Ukraine war, where known cyber operations have directly contributed to the conflict, those involved in the Israel-Hamas conflict have not directly contributed to Hamas’ military operations against Israel,” the company stated in its “2024 Global Threat Report” released on Feb. 21.
Building Rapport Over Time
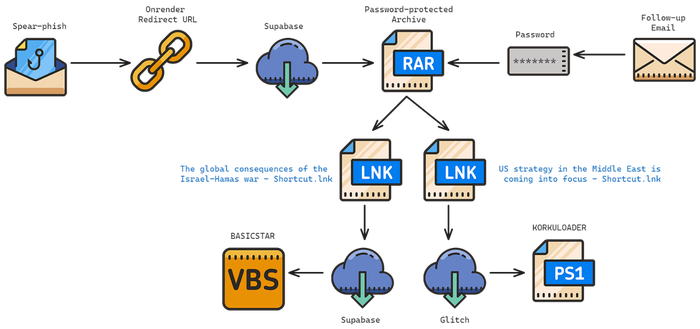
These attacks usually start with spear-phishing and end with a combination of malware delivered to the target’s system, according to an advisory from Volexity, which calls the group CharmingCypress. In September and October 2023, CharmingCypress used a number of typo-squatted domains — addresses similar to legitimate domains — to pose as officials from the International Institute of Iranian Studies (IIIS) to invite policy experts to a webinar. The initial email demonstrated the low-and-slow approach of CharmingCypress, eschewing any malicious link or attachment and inviting the targeted professional to reach out through other channels of communications, such as WhatsApp and Signal.
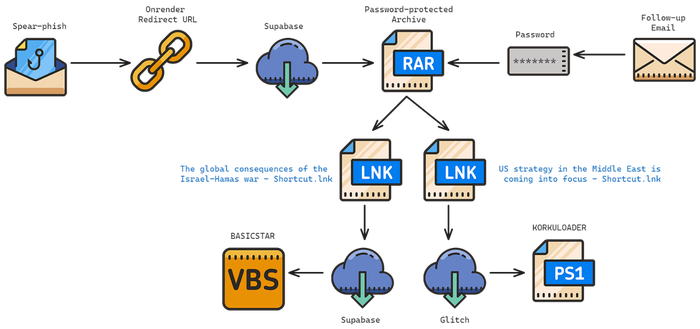
Using in-depth spearphishing, CharmingCypress aims to convince policy experts to install malware. Source: Volexity
The attacks target Middle East policy experts worldwide, with Volexity encountering a majority of attacks against European and US professionals, Adair says.
“They are quite aggressive,” he says. “They’ll even set up entire email chains or a phishing scenario where they’re looking for comment and there’s other people — maybe three, four, or five people on that email thread with the exception of the target — they’re definitely trying to build rapport.”
The long con eventually delivers a payload. Volexity identified five different malware families associated with the threat. The PowerLess backdoor is installed by the Windows version of the malware-laden virtual private network (VPN) application, which uses PowerShell to allow files to be transferred and executed, as well as targeting specific data on the system, logging keystrokes, and capturing screenshots. A macOS version of the malware is dubbed NokNok, while a separate malware chain using a RAR archive and LNK exploit leads to a backdoor named Basicstar.
Defending Becomes More Difficult
The group’s approach to social engineering definitely embodies the “persistence” piece of the advanced persistent threat (APT). Volexity sees a “constant barrage” of attacks, so policy experts have to become even more suspicious of cold contacts, Adair says.
Doing so will be difficult, as many policy experts are academics in constant contact with students or members of the public and are not used to being strict with their contacts, he says. Yet they should definitely think before opening documents or entering credentials into a site reached through an unknown link.
“At the end of the day, they have to get the person to click something or open something, which if I want you to review a paper or something like that, means … being very wary of links and files,” Adair says. “If I have to enter my credentials at any point in time, or authorize something — that should be a major red flag. Similarly, if I’m being asked to download something, that should be a pretty big red flag.”
In addition, policy experts need to understand that CharmingCypress will continue to target them even if its attempts fail, Volexity stated.
“This threat actor is highly committed to conducting surveillance on their targets in order to determine how best to manipulate them and deploy malware,” the company stated in its advisory. “Additionally, few other threat actors have consistently churned out as many campaigns as CharmingCypress, dedicating human operators to support their ongoing efforts.”
- SEO Powered Content & PR Distribution. Get Amplified Today.
- PlatoData.Network Vertical Generative Ai. Empower Yourself. Access Here.
- PlatoAiStream. Web3 Intelligence. Knowledge Amplified. Access Here.
- PlatoESG. Carbon, CleanTech, Energy, Environment, Solar, Waste Management. Access Here.
- PlatoHealth. Biotech and Clinical Trials Intelligence. Access Here.
- Source: https://www.darkreading.com/vulnerabilities-threats/iran-backed-charming-kitten-stages-fake-webinar-platform-to-ensnare-targets
- :has
- :is
- :not
- :where
- $UP
- 2013
- 2023
- 2024
- 7
- 9
- a
- academics
- access
- According
- Accounts
- active
- actors
- addition
- Additionally
- addresses
- advanced
- advisory
- against
- agencies
- aggressive
- aims
- allow
- also
- an
- and
- any
- Application
- applications
- approach
- APT
- Archive
- ARE
- areas
- AS
- aspect
- associated
- At
- attack
- Attacks
- Attempts
- authorize
- average
- backdoor
- barrage
- BE
- become
- becomes
- been
- before
- being
- BEST
- between
- Big
- build
- Building
- but
- by
- Calls
- Campaign
- Campaigns
- Capturing
- chain
- chains
- channels
- click
- Co-founder
- cold
- combination
- comment
- committed
- Communications
- Companies
- company
- compromise
- Compromised
- conducted
- conducting
- confidence
- conflict
- consistently
- constant
- contact
- contacts
- continue
- contributed
- convince
- corps
- covering
- Credentials
- crosshairs
- cyber
- Cybersecurity
- data
- day
- dedication
- Defending
- definitely
- delivered
- delivers
- demonstrated
- deploy
- described
- Determine
- developed
- different
- difficult
- directly
- documents
- domains
- don
- download
- dubbed
- East
- effort
- efforts
- emails
- embodies
- embraced
- encountering
- end
- Engineering
- Engineers
- Enter
- entering
- Entire
- Europe
- European
- Even
- eventually
- example
- exception
- executed
- experts
- Exploit
- exploitation
- extensive
- FAIL
- fake
- families
- Feb
- few
- Files
- Firm
- five
- flow
- following
- For
- four
- frequently
- from
- Gain
- game
- gather
- geopolitical
- get
- Global
- Go
- Government
- government agencies
- Group
- Group’s
- Guard
- had
- hamas
- Have
- he
- highly
- How
- HTTPS
- human
- i
- identified
- identify
- if
- image
- in
- in-depth
- incident
- incident response
- Including
- initial
- install
- installation
- installed
- installing
- Institute
- Intelligence
- interest
- International
- into
- invite
- inviting
- involved
- Iranian
- Islamic
- Israel
- IT
- ITS
- January
- Jordan
- Journalists
- Know
- known
- latest
- Lawyers
- Leads
- least
- legitimate
- Level
- like
- LINK
- links
- ll
- logging
- Long
- looking
- Lot
- macos
- made
- major
- Majority
- malicious
- malware
- many
- Margin
- maybe
- means
- Members
- Microsoft
- Middle
- Middle East
- Military
- mint
- Month
- more
- much
- my
- Named
- necessarily
- Need
- network
- nongovernmental
- number
- october
- of
- officers
- officials
- often
- on
- ongoing
- open
- opening
- Operations
- operators
- or
- order
- organizations
- Other
- out
- over
- overall
- Paper
- patient
- Pegasus
- People
- persistence
- person
- phishing
- phony
- piece
- platform
- plato
- Plato Data Intelligence
- PlatoData
- Point
- policy
- political
- pose
- PowerShell
- president
- pretty
- private
- professional
- professionals
- public
- published
- quickly
- quite
- RE
- reach
- reached
- recently
- Red
- region
- released
- report
- reportedly
- researchers
- response
- resulting
- review
- revolutionary
- Russia-Ukraine War
- s
- says
- scenario
- screenshots
- security
- sees
- send
- separate
- September
- Services
- set
- should
- Signal
- significant
- similar
- Similarly
- since
- site
- Sites
- skilled
- So
- Social
- Social Engineering
- some
- something
- sophisticated
- Source
- specific
- Sponsored
- spyware
- stages
- start
- stated
- steven
- Strict
- Students
- studies
- such
- support
- surveillance
- suspicious
- system
- tactics
- Tanks
- Target
- targeted
- targeting
- targets
- tensions
- than
- that
- The
- their
- Them
- then
- There.
- they
- think
- this
- those
- threat
- threat actors
- Threat Report
- three
- Through
- time
- to
- Topics
- transferred
- trying
- Ukraine
- Uncommon
- understand
- unknown
- unlike
- us
- used
- users
- uses
- using
- usually
- version
- very
- Victim
- victims
- Virtual
- VPN
- want
- war
- webinar
- WELL
- which
- while
- whose
- will
- windows
- with
- worldwide
- yet
- You
- Your
- zephyrnet