WESTFORD, Massachusetts,
27 Septembrie, 2022 — NETSCOUT
SYSTEMS, INC. (NASDAQ: NTCT) today announced findings from its 1H2022 DDoS Threat Intelligence Report. The findings demonstrate how sophisticated cybercriminals
have become at bypassing defenses with new DDoS attack vectors and successful methodologies.
“By constantly innovating and adapting, attackers
are designing new, more effective DDoS attack vectors or doubling down on existing effective methodologies,” said Richard Hummel, threat intelligence lead, NETSCOUT. “In the first half of 2022, attackers conducted more pre-attack reconnaissance, exercised
a new attack vector called TP240 PhoneHome, created a tsunami of TCP flooding attacks, and rapidly expanded high-powered botnets to plague network-connected resources. In addition, bad actors have openly embraced online aggression with high-profile DDoS attack
campaigns related to geopolitical unrest, which have had global implications.”
NETSCOUT’s Active Level Threat Analysis System (ATLAS™)
compiles DDoS attack statistics from most of the world’s ISPs, large data centers, and government and enterprise networks. This data represents intelligence on attacks occurring in over 190 countries, 550 industries, and 50,000 autonomous system numbers (ASNs).
NETSCOUT’s ATLAS Security Engineering and Response Team (ASERT) analyzes and curates this data to provide unique insights in its biannual report. Key findings from the 1H2022 NETSCOUT DDoS Threat Intelligence Report include:
- Au existat 6,019,888 de atacuri globale DDoS în 1st jumătate din 2022.
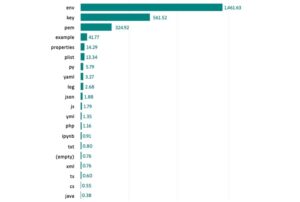
- Atacurile de inundații bazate pe TCP (SYN, ACK, RST) rămân cel mai utilizat vector de atac, aproximativ 46% din toate atacurile continuând o tendință care a început la începutul anului 2021.
- Atacurile de tortură cu apă DNS s-au accelerat în 2022, cu o creștere de 46%, în principal utilizând inundațiile de interogări UDP, în timp ce atacurile cu bombă de covor au cunoscut o revenire majoră spre sfârșitul celui de-al doilea trimestru; per total, atacurile de amplificare a DNS au scăzut cu 31% din 2H2021 până în 1H2022.
- Noul vector DDoS de reflectare/amplificare TP240 PhoneHome a fost descoperit la începutul anului 2022, cu un raport de amplificare record de 4,293,967,296:1; acțiunile rapide au eradicat natura abuzabilă a acestui serviciu.
- Proliferarea rețelelor botnet malware a crescut într-un ritm alarmant, cu 21,226 de noduri urmărite în primul trimestru până la 488,381 de noduri în al doilea, rezultând mai multe atacuri directe la nivel de aplicație.
Tulburările geopolitice generează atacuri DDoS crescute
As Russian ground troops entered Ukraine in late February, there was a significant uptick in DDoS attacks targeting governmental departments, online media
organizations, financial firms, hosting providers, and cryptocurrency-related firms, as
documentat anterior.
However, the ripple effect resulting from the war had a dramatic impact on DDoS attacks in other countries including:
- Irlanda a cunoscut o creștere a atacurilor după ce a furnizat servicii organizațiilor ucrainene.
- India experienced a measurable increase in DDoS attacks following its abstention from the UN Security Council and General Assembly votes condemning Russia’s actions in Ukraine.
- În aceeași zi, Taiwan a suportat cel mai mare număr de atacuri DDoS după ce a făcut declarații publice în sprijinul Ucrainei, la fel ca și în Belize.
- Finlanda a înregistrat o creștere de 258% a atacurilor DDoS de la an la an, coincizând cu anunțul său de a solicita aderarea la NATO.
- Polonia, România, Lituania și Norvegia au fost vizate de atacuri DDoS legate de Killnet; un grup de atacatori online aliniați cu Rusia.
- While the frequency and severity of DDoS attacks in North America remained relatively consistent, satellite telecommunications providers experienced an increase in high-impact DDoS attacks, especially after providing support for Ukraine’s communications infrastructure.
- Rusia a cunoscut o creștere de aproape 3 ori a atacurilor zilnice DDoS de când a început conflictul cu Ucraina și a continuat până la sfârșitul perioadei de raportare.
Similarly, as tensions between Taiwan, China, and Hong Kong escalated in 1H2022, DDoS attacks against Taiwan regularly occurred in concert with related public
evenimente.
nemaivăzut
Inteligență
No other vendor sees and knows more about DDoS attack activity and best practices in attack protection than NETSCOUT.
In addition to publishing the DDoS Threat Intelligence Report, NETSCOUT also presents its highly curated real-time DDoS attack data on its
Omnis Threat Horizon portal
to give customers visibility into the global threat landscape and understand the impact on their organizations. This data also fuels NETSCOUT’s ATLAS Intelligence Feed (AIF) which continuously arms NETSCOUT’s Omnis and Arbor security portfolio. Together with
AIF, the Omnis and Arbor products automatically detect and block threat activity for enterprises and service providers worldwide.
Vizitaţi nostru
site web interactiv
for more information on NETSCOUT’s semi-annual DDoS Threat Intelligence Report. You can also find us on
Facebook,
LinkedIn,
și
Twitter pentru actualizări privind amenințările și cele mai recente tendințe și perspective.
Despre NETSCOUT
NETSCOUT SYSTEMS, INC. (NASDAQ: NTCT) protects the connected world from cyberattacks and performance disruptions through advanced network detection and response
and pervasive network visibility. Powered by our pioneering deep packet inspection at scale, we serve the world’s largest enterprises, service providers,
and public sector organizations. Learn more at www.netscout.com or
follow @NETSCOUT on LinkedIn, Twitter, or Facebook.
- blockchain
- portofele de criptare
- criptoschimb
- securitate cibernetică
- cybercriminals
- Securitate cibernetică
- Lectură întunecată
- Departamentul de Securitate Națională
- portofele digitale
- firewall
- Kaspersky
- malware
- McAfee
- NexBLOC
- Plato
- platoul ai
- Informații despre date Platon
- Jocul lui Platon
- PlatoData
- platogaming
- VPN
- securitatea site-ului